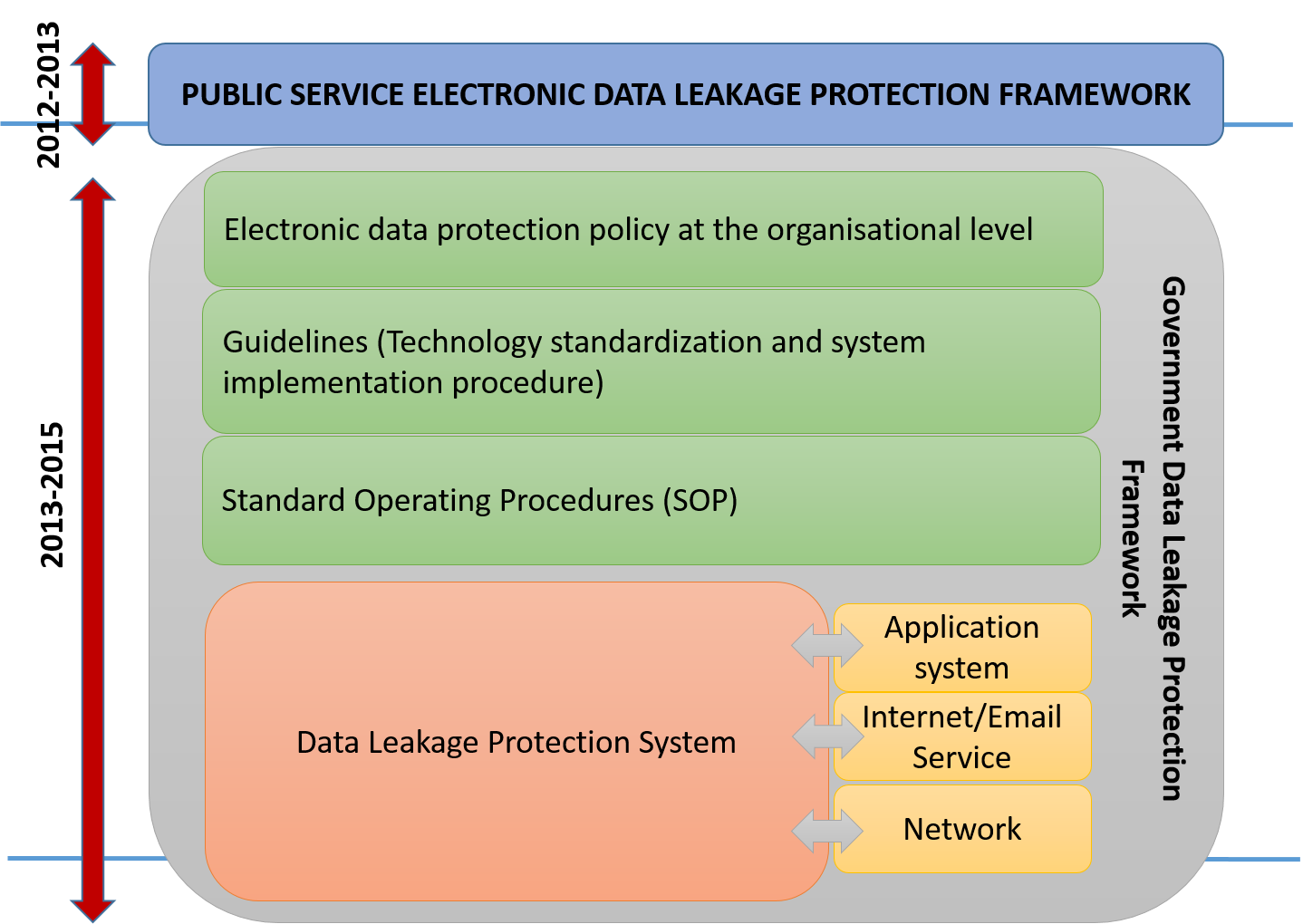
MyGOV - Cyber Security And Disaster Response And Recovery | Cyber Security | Data Leakage Protection - DLP

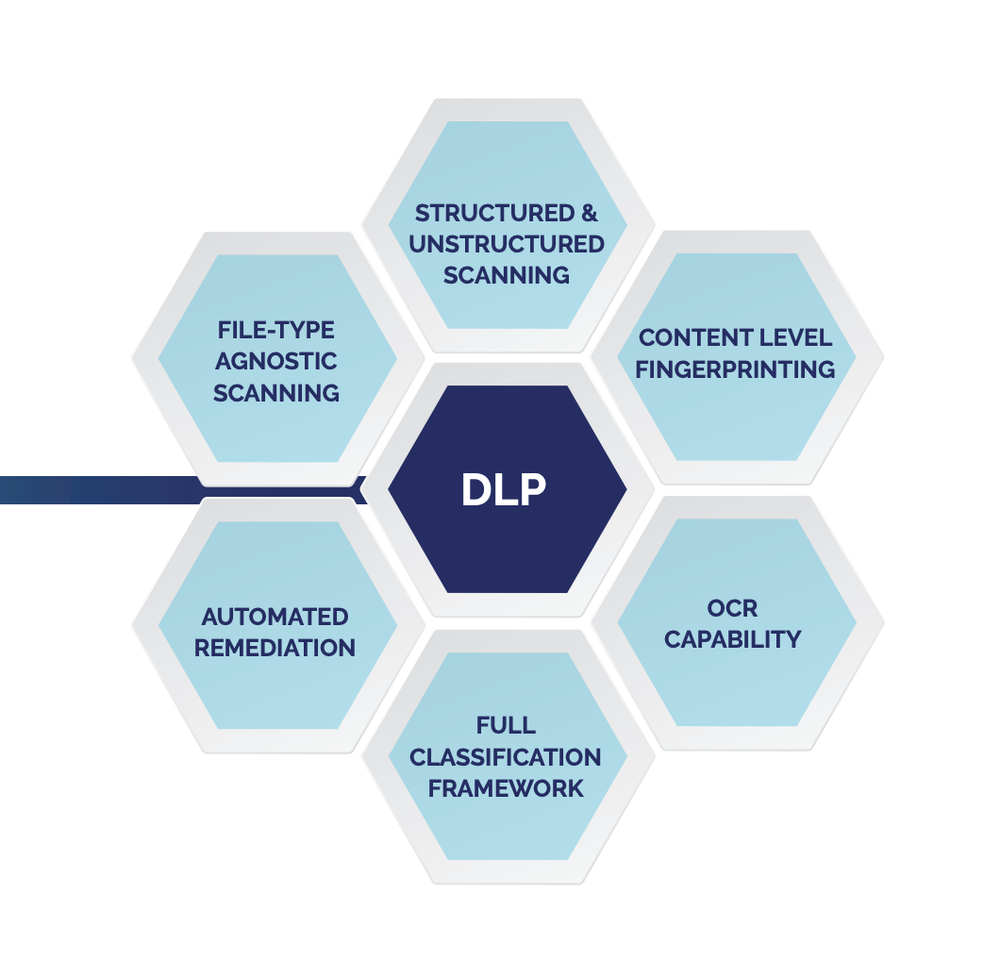
Cloud security framework and key management services collectively for implementing DLP and IRM - ScienceDirect

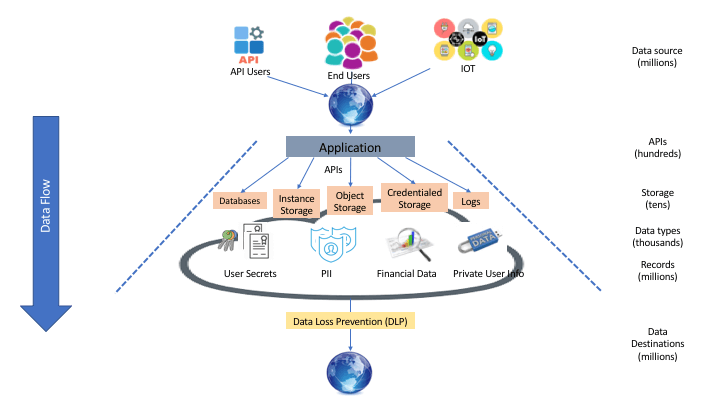
Example architecture for using a DLP proxy to query a database containing sensitive data | Cloud Architecture Center | Google Cloud










.png)


