Data Mining: How to Protect Patient Privacy and Security When Using Data - Electronic Health Reporter

Data Warehousing and Data Mining Techniques for Cyber Security (Advances in Information Security, 31): Singhal, Anoop: 9780387264097: Amazon.com: Books
Data-Mining and Analytics: Rising Concerns over Privacy and People's Security | Public Opinion and Voting Behavior | APSA Preprints | Cambridge Open Engage

Privacy and Security Issues in Data Mining and Machine Learning: International ECML/PKDD Workshop, PSDML 2010, Barcelona, Spain, September 24, 2010. Revised Selected Papers | SpringerLink
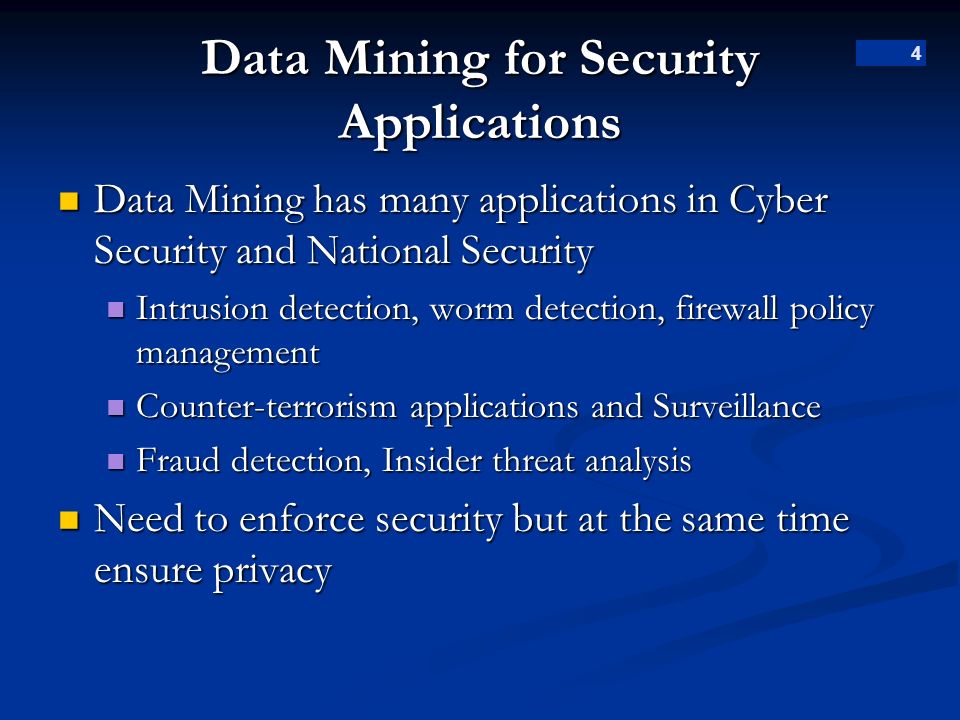
1 Data Mining for Surveillance Applications Suspicious Event Detection Dr. Bhavani Thuraisingham April ppt download